Mastering the Cybersecurity Interview: The Five Decisive Questions
Mastering Cyber Security Interview
Hey,
Quick check: did you take one action from last week's 7-Day Kickstart? If you installed Kali, completed a TryHackMe room, or pushed something to GitHub — you're already ahead of most people reading this. If you didn't, no judgment. This issue will give you something different to act on.
This week, I'm giving you the five interview questions I ask every cybersecurity candidate — and the exact structure that separates the people I hire from the people I don't.
🔥 THIS WEEK'S INSIGHT: The 5 Questions That Decide Everything
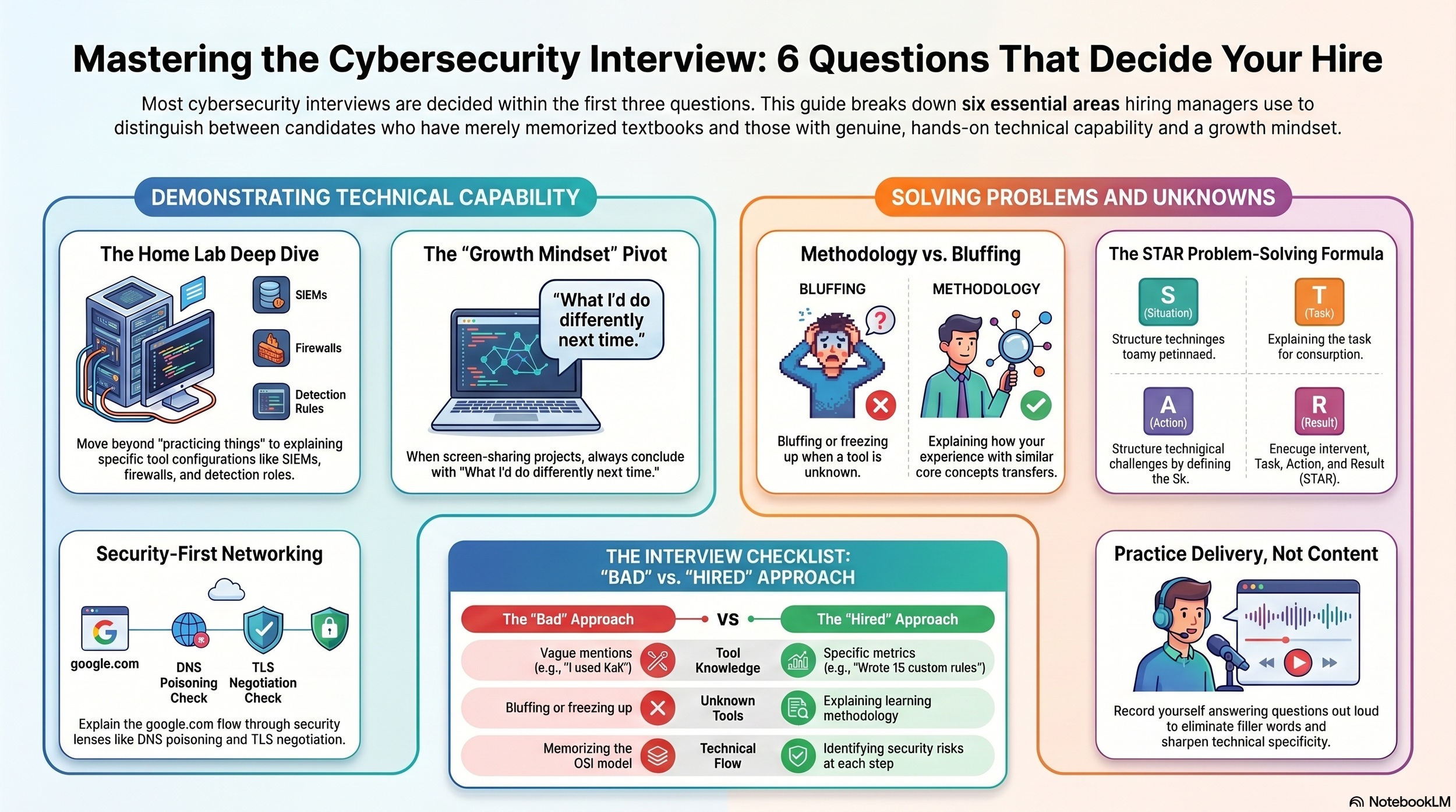
I've sat across the table from hundreds of candidates. And here's the uncomfortable truth: most interviews are decided within the first three questions. Not because hiring managers are impatient — because the first three answers reveal whether a candidate has real capability or just memorised a textbook.
Here are the five questions, why I ask them, and how to answer them.
Question 1: "Walk me through your home lab."
Why I ask it: This is the "show me, don't tell me" question. I don't care about certifications at this point. I want to know: did you build something? Can you explain it? Do you understand your own work?
Bad answer: "I set up VirtualBox with Kali and a Windows machine and practised some things."
That tells me nothing. What things? Why? What did you learn?
Good answer: "I built a four-machine environment. Kali attack box, Windows Server endpoint, Wazuh SIEM, and pfSense firewall. I configured Wazuh to collect Windows event logs and Sysmon data, then wrote 15 custom detection rules targeting brute force attacks, suspicious PowerShell execution, and privilege escalation. I validated each rule by launching the corresponding attack from Kali and confirming the alert fired correctly. The biggest lesson? How noisy a real SIEM is. Tuning false positives taught me more about real SOC work than any course."
That answer took 30 seconds. It mentioned specific tools, specific numbers, a specific insight, and demonstrated actual understanding. Everything is backed by a GitHub link.
Question 2: "Can you show me one of your projects?" (Screen Share)
Why I ask it: I want to see how you navigate your own work under pressure. Can you find things quickly? Can you explain architecture decisions? Do you understand what you built, or did you follow a tutorial and forget it?
The move: Open your GitHub. Show the README first — that's your 30-second pitch. Then walk through the architecture diagram. Then show one specific thing you're proud of: a detection rule, a Terraform module, a Python script.
The key phrase: "What I'd do differently next time is..."
That single phrase tells me you're reflective, not just capable. It shows growth mindset. I've hired people specifically because they could articulate what they'd improve.
Question 3: "What happens when you type google.com into your browser?"
Why I ask it: This is the technical foundation test. If you can walk through DNS resolution, TCP handshake, TLS negotiation, and HTTP request/response — I know you understand networking at a fundamental level.
The structure: DNS lookup → TCP three-way handshake → TLS handshake → HTTP GET request → server response → browser renders.
The security angle that wins: "At each step, there's a security implication. DNS can be poisoned. The TCP connection can be hijacked. Without TLS, the traffic is readable. The HTTP response could contain malicious content. Understanding the flow means understanding where to defend it."
That last part elevates your answer from "I memorised the OSI model" to "I think like a security professional."
Question 4: "Have you used [specific tool they mention]?"
When you haven't? This is where most candidates fail. They bluff. Or they freeze. Both are wrong.
The answer: "I haven't used [tool] directly, but in my home lab I set up [similar tool] and worked with the same core concepts — log ingestion, correlation, and rule-based alerting. The principles transfer across platforms. If the role requires [tool], I'd start with their free training and spin up a trial environment. That's exactly how I learned [similar tool] in about two weeks."
This answer is BETTER than a bluff. It shows methodology: how you learn predicts how you'll perform. I'd rather hire someone who says "I don't know, but here's how I'd figure it out" over someone who pretends.
Question 5: "Tell me about a time you solved a difficult technical problem."
Why I ask it: Behavioural questions reveal your process, not just your knowledge. I'm listening for: how you approach unfamiliar problems, whether you ask for help or go it alone, and whether you can structure a clear narrative under pressure.
The STAR formula: Situation → Task → Action → Result.
Example from a home lab: "During my SIEM lab build, Wazuh wasn't receiving any logs from the Windows endpoint. I checked the agent status — running. Checked the firewall — port 1514 was open. The issue turned out to be a DNS resolution problem between the VMs. The agent was trying to resolve the Wazuh server by hostname instead of IP. I fixed it by updating the agent config to use the static IP, documented the troubleshooting steps, and wrote a README note so anyone using my lab guide wouldn't hit the same issue."
Real problem. Structured answer. Shows debugging methodology. References documentation. All from a home lab — no professional experience required.
📰 ONE THING HAPPENING IN CYBERSECURITY THIS WEEK
Deepfake attacks on businesses are accelerating. A growing number of organisations have reported AI-generated video calls being used for social engineering — attackers impersonating executives on live video to authorise financial transfers or credential sharing.
What this means for you: AI security knowledge is no longer optional at any level. If you can explain what a deepfake is, how it's generated, and what detection strategies exist, you have an answer for the interview question nobody else in the room can handle: "What emerging threats concern you most?"
Study the OWASP Top 10 for LLMs this weekend. Free. Two hours. It'll give you vocabulary that 95% of candidates don't have.
🛠️ FREE TOOL OF THE WEEK: CyberDefenders
What it is: A free platform offering real-world DFIR (Digital Forensics and Incident Response) challenges using actual evidence — packet captures, memory dumps, and disk images.
Why it matters: CyberDefenders challenges aren't simulations. They're real forensic artefacts from real incidents. Completing them gives you investigation experience that translates directly to SOC and DFIR interviews.
Where to get it: cyberdefenders.org — start with the "CyberCorp Case" or "Insider" challenges.
Portfolio move: Complete a challenge, write up your investigation process (what you found, what tools you used, what the evidence showed), and publish it on GitHub or as a blog post. Reference it in interviews as investigation experience.
💡 CAREER ADVICE FROM THE HIRING TABLE
Practice your interview answers out loud. Not in your head. Out loud.
Recording yourself answering "Walk me through your home lab" on your phone and watching it back is the most uncomfortable and most effective interview preparation that exists. You'll immediately notice: filler words, vague phrasing, missing details, and moments where you lose your thread.
Do this five times for each of the five questions above. By the sixth attempt, your answers are tight, confident, and natural.
Most candidates study content. The candidates who get hired practise delivery.
📺 FROM THE CHANNEL THIS WEEK
New video: If you haven't decided which cybersecurity career to pursue, the new "Which Cybersecurity Career Is Right for You?" video walks you through every path based on your personality — detective, builder, strategist, or breaker. It's designed to end the indecision.
Deep dive on interviews: The full Cybersecurity Interview Masterclass covers 8 questions in detail, including the "I don't know" survival technique and a live screen-share demonstration. If this newsletter gave you the overview, the video gives you the full training.
Both are on the channel → YouTube: @mpcybersecurity
Downloadable skill matrices for every career path are on the website → mpcybersecurity.co.uk
🎯 YOUR ONE ACTION THIS WEEK
Open your phone's voice recorder. Answer this question out loud:
"Walk me through your home lab."
If you have a lab, explain it as if I'm sitting across the table. Record it. Listen back. Was it specific? Did you mention tools by name? Did you include a number (how many detection rules, how many machines, how many exercises)?
If you don't have a lab yet, your action is different: download the SOC Home Lab Build Guide from the website and build it this weekend. Next week when I ask you to practise this answer, you'll have something real to talk about.
One action. That's the deal. Every week.
🔜 COMING NEXT WEEK
Issue #3: "The Home Lab That Gets You Hired" — I'll break down exactly what a hiring manager looks for in a home lab portfolio, the three mistakes that make your lab look amateur, and the one documentation approach that makes your GitHub stand out from every other candidate.
If you know someone preparing for cybersecurity interviews, forward this email to them. It costs nothing and might be the difference between a rejection and an offer.
See you next week.
Marius Poskus Global VP of Cybersecurity / CISO CTRL+ALT+DEFEND
→ YouTube: youtube.com/@mpcybersecurity
→ LinkedIn: linkedin.com/in/marius-poskus
→ Website: mpcybersecurity.co.uk
→ TikTok: @mariusposkus0
You are struggling to land cyber security interviews? Not sure if this is your CV fault? Let the professional cyber security expert with 10 years worth of experience roast your CV. Once you have made the purchase I will send you an email for CV submission, feedback sent back within 3 business days