The Cybersecurity Career Newsletter
Cyber Security career fast-track blueprint
Issue #1 — Welcome Edition
Hey,
Welcome to CTRL+ALT+DEFEND Weekly.
You're here because you downloaded one of our career blueprints or skill matrices. Which means you're serious about breaking into cybersecurity — not just "thinking about it."
I'm Marius. I'm a CISO at a financial services company, a vCISO consultant, and I run the CTRL+ALT+DEFEND YouTube channel. I've hired cybersecurity professionals across multiple regions and reviewed more CVs than I can count. Every week, I'm going to share one insight from the hiring side of the table that you can act on immediately.
No filler. No upsells disguised as advice. Just the things I actually tell people in real conversations.
Let's start.
🔥 THIS WEEK'S INSIGHT: The 7-Day Kickstart
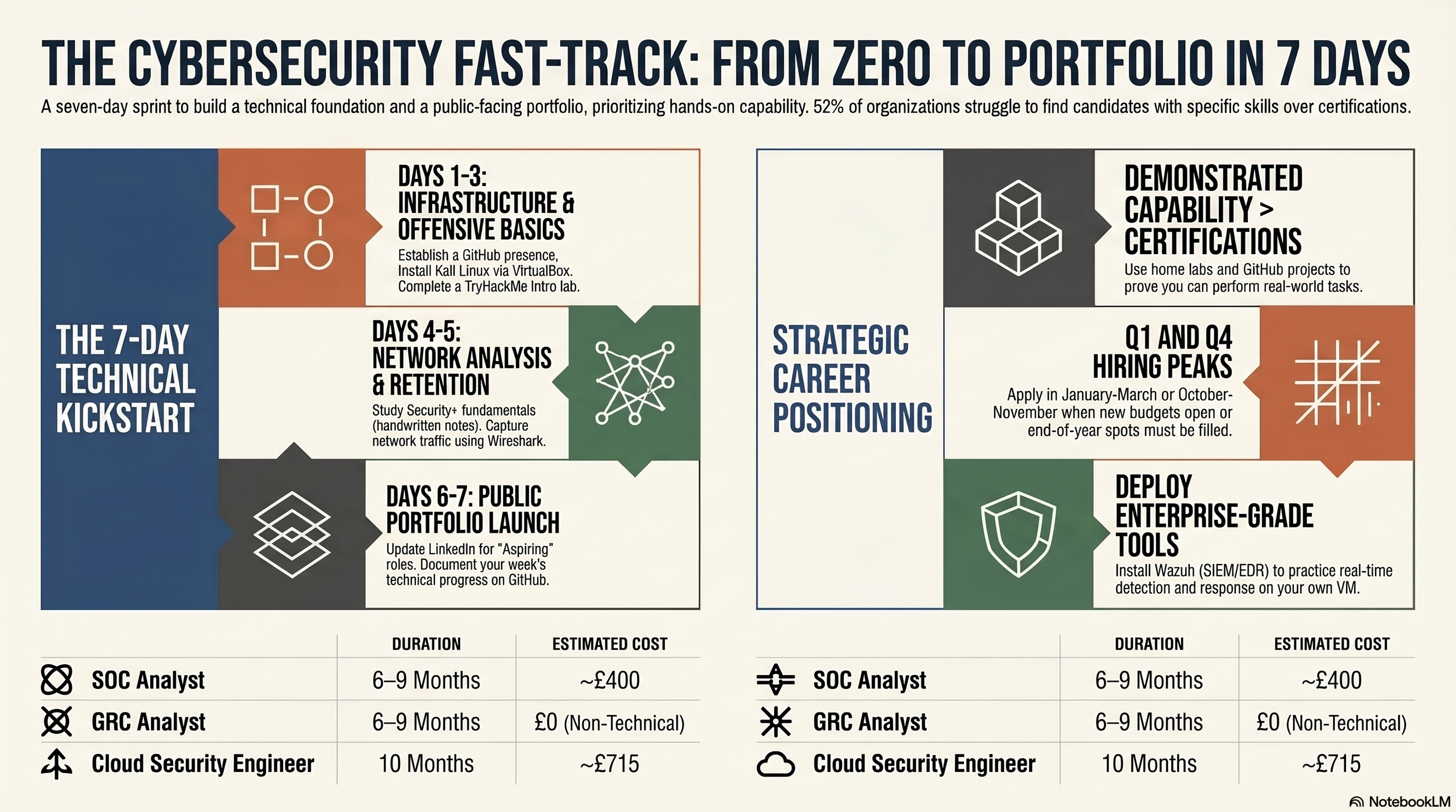
If I was starting from scratch in cybersecurity today, here's exactly what I'd do in my first seven days. Not seven months. Seven days.
Day 1 (Monday): Create a GitHub account. Set up your profile with a professional photo, a one-line bio ("Building cybersecurity skills | Security+ in progress"), and pin an empty repository called "cybersecurity-journey." You'll fill it later. The account exists now. That matters.
Day 2 (Tuesday): Install VirtualBox on your computer (free from virtualbox.org). Download the Kali Linux VM image (free from kali.org). Import it. Boot it up. Open a terminal. Type whoami. Congratulations — you just used a real offensive security operating system.
Day 3 (Wednesday): Create a TryHackMe account (free tier). Complete the "Introduction to Cyber Security" room. It takes about an hour. Take a screenshot of your completion badge.
Day 4 (Thursday): Watch the first section of Professor Messer's Security+ SY0-701 course on YouTube (free). Take handwritten notes. Not typed — handwritten. Studies show retention increases by 30% with handwriting.
Day 5 (Friday): Go back to your Kali Linux VM. Open Wireshark. Capture 60 seconds of network traffic. You won't understand most of it yet. That's fine. The point is you've now used two real security tools in one week.
Day 6 (Saturday): Update your LinkedIn headline from whatever it says now to: "Aspiring Cybersecurity Analyst | Security+ In Progress | Building Hands-On Skills." Post a short update: "Day 6 of my cybersecurity journey. Set up my first Kali Linux VM and completed my first TryHackMe room. Long way to go but I've started." Tag #cybersecurity #careerchange.
Day 7 (Sunday): Go back to that GitHub repository. Add a README.md file. Write three sentences: what you're learning, what tools you've used this week, and what you plan to do next. Push it. Your portfolio has officially begun.
Seven days. Zero cost. And you've now done more than 90% of people who say they want to get into cybersecurity.
📰 ONE THING HAPPENING IN CYBERSECURITY THIS WEEK
The ISC2 2025 Workforce Study confirmed a fundamental shift: for the first time, more organisations (52%) said their biggest challenge is finding people with the right skills — not just finding enough people.
What this means for you: certifications alone won't get you hired. The market has moved from "hire for headcount" to "hire for demonstrated capability." Your home lab, your GitHub projects, and your ability to walk through them in an interview now matter more than the number of certs on your CV.
Your action: if you have certifications but no portfolio, this week's priority is building one project — any project — and documenting it on GitHub with a professional README.
🛠️ FREE TOOL OF THE WEEK: Wazuh
What it is: A free, open-source SIEM (Security Information and Event Management) and EDR (Endpoint Detection and Response) platform.
Why it matters: Wazuh is the same category of tool that enterprise SOCs use daily. Having "Wazuh SIEM" on your CV demonstrates you've worked with real detection and response technology, not just studied it from textbooks.
Where to get it: wazuh.com — the quickstart guide deploys the entire platform on a single Ubuntu VM in under 30 minutes.
What to do with it: Install it in your home lab. Connect a Windows VM as an endpoint. Watch security events flow into the dashboard in real time. Write your first detection rule (start with failed login attempts — Event ID 4625).
Portfolio move: Screenshot the dashboard showing your custom rule firing, add it to your GitHub with a brief explanation of what the rule detects and why it matters.
💡 CAREER ADVICE FROM THE HIRING TABLE
Here's something I rarely see discussed: the best time to apply for cybersecurity jobs is Q1 (January–March) and Q4 (October–November).
Q1 is when companies receive new annual budgets and open headcount. Q4 is when managers rush to fill roles before year-end budget deadlines.
Summer (June–August) is typically the slowest hiring period. If you're timing your job search, aim to be application-ready by September so you're in full job-hunt mode when Q4 hiring ramps up.
Plan backwards from your target application date. If you want to be ready by October, start your Security+ study now. Build your home lab in the summer. Have your portfolio polished by September.
Timing isn't everything. But it helps.
📺 FROM THE CHANNEL THIS WEEK
If you haven't explored the full blueprint series yet, here's the current library — all free, all on YouTube:
→ SOC Analyst Blueprint — The most common entry point. 6–9 months. ~£400.
→ GRC Analyst Blueprint — The non-technical path. No coding required. 6–9 months.
→ Cloud Security Engineer Blueprint — Highest-paid technical path. 10 months. ~£715.
→ DevSecOps Engineer Blueprint — Secure the pipeline. 12–14 months.
→ Penetration Tester Blueprint — Hardest path, highest reward. 12–18 months.
→ IAM Security Analyst Blueprint — The secret gem nobody talks about. 10–12 months.
→ How to Secure AI — The emerging skill every professional needs.
→ Interview Masterclass — Exact answers that get you hired.
Each blueprint has a downloadable skill matrix on the website with every skill, certification, tool, timeline, and cost mapped out. If you haven't grabbed yours yet, they're at [mpcybersecurity.co.uk].
🎯 YOUR ONE ACTION THIS WEEK
Pick one thing from this newsletter. Just one. And do it before next week's email arrives.
Install Kali Linux. Complete a TryHackMe room. Watch one Professor Messer section. Update your LinkedIn headline. Push a README to GitHub.
One action. That's all I'm asking. The people who act on one thing per week for 6 months are the ones who end up in my interview room with a portfolio that makes me stop scrolling.
🔜 COMING NEXT WEEK
Next issue: "The 5 Interview Questions Every Cybersecurity Hiring Manager Asks (And The Answers That Get You Hired)" — pulled directly from the Interview Masterclass. I'll break down the exact questions, the bad answers I hear constantly, and the good answers that make candidates memorable.
If someone you know is trying to break into cybersecurity, forward this email to them. It costs nothing and might change their trajectory.
See you next week.
Marius Poskus Global VP of Cybersecurity / CISO CTRL+ALT+DEFEND
→ YouTube: youtube.com/@mpcybersecurity
→ LinkedIn: linkedin.com/in/marius-poskus
→ Website: mpcybersecurity.co.uk